Seeking a solution for the WordPress redirect hack? 👨💻
The WordPress redirect hack is unfortunately a common occurrence and it’s also one of the worst malware infections a website can experience.
In this type of hack, your site’s visitors are redirected to malicious websites 🦇 where they are exploited at the expense of your site’s reputation.
Other negative impacts of it are loss of organic traffic, high bounce rate, and SEO penalties.
👉 The best way to contain the damages caused by a redirect hack is to clean your website immediately and take solid steps to prevent future threats.
By the end of this article, you’ll know how to remove the hack from your WordPress website and implement steps to protect your site from future hack attacks.
Let’s dive in. 🥽
Causes, impact, identification, and variation of a WordPress redirect hack
A WordPress redirect hack occurs when hackers gain access to your website and inject malware into your files and folders.
What can cause the WordPress redirect hack?
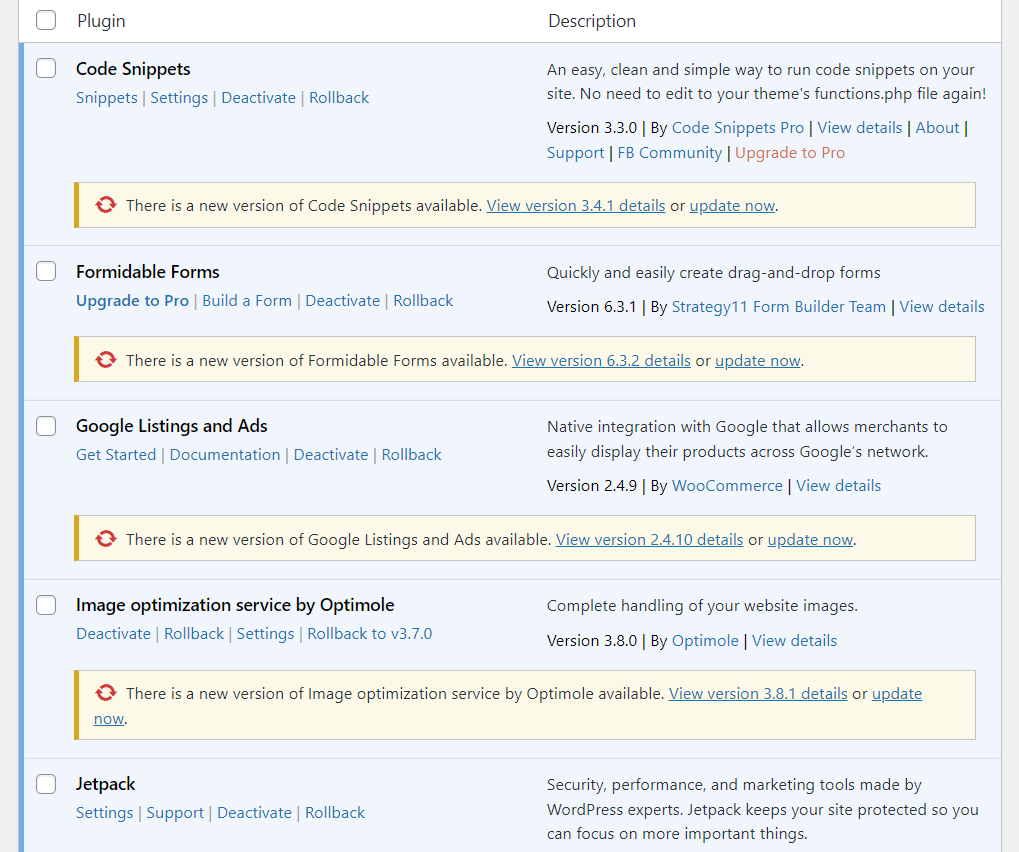
Hackers normally gain unauthorized access to WordPress websites by exploiting outdated or nulled themes and plugins, as well as guessing weak user credentials.
What are the impacts of the WordPress redirect hack?
After gaining access to your website, hackers infect your files and folders with malicious code that can cause some/all of your pages to redirect visitors to nefarious websites.
In some cases, the hackers will make it so that logged-in admin users don’t experience the redirect, which means you might not even know that anything is wrong.
These sites are run by hackers and they are built to dupe redirected visitors into buying illegal products or to trick them into giving up personal (like medical and financial) information.
Some visitors are smart enough to recognize these redirections as spam and they leave these nefarious websites immediately. But they also start perceiving your brand negatively and may decide to stop visiting your website.
Visitors who end up getting exploited will never return to your website and they might declare your site as a fraud in online forums and social media groups, further tarnishing your brand.
Websites with poor reputations don’t draw a lot of visitors, so you are bound to see a massive drop in your traffic. 📉
Soon enough, search engines will notice your site’s high bounce rates (caused by redirection) and conclude that your website is not offering value to visitors. So, they will decide to drop your rankings. After they find out that your site is hacked, search engines will penalize your site and prevent users from accessing it, which will cause a further decline in traffic.
Even your hosting provider will suspend your site when it detects malware infection on your WordPress website.
In addition to all this, hackers have access to confidential information regarding your business, user data, trade secrets, pricing information, etc. They may end up stealing this information and selling it to your competitors to make a few quick bucks. 🤑
How to identify the WordPress redirect hack?
The obvious symptom of a WordPress redirection hack is when users and visitors are being redirected to strange spammy websites. Other signs of this type of hack are:
- Your site’s URL appears on the search engine but visitors trying to open the URL are redirected to a malicious site
- Push notifications or CAPTCHAs appear on your website without your knowledge. Visitors trying to opt-in or verify are redirected to other sites
- Suspicious bit.ly links appear on pages and posts. Clicking on these links causes redirections
- Unknown files and folders with gibberish names appear on your site’s server
- Also, new posts and pages are published without your knowledge. When you try to open them, you are redirected to malicious websites
WordPress redirect hack variations
Based on how users and visitors are being redirected, the WordPress redirect hack can be divided into different types. Let’s take a look at the redirection hack types or variations:
- Push notification redirection hack: Visitors are shown a push notification window that redirects them to adult websites.
- Device-specific redirection hack: Appears only on the mobile or desktop version of the website.
- Location-specific redirection hack: Visitors from only certain locations are redirected to nefarious sites.
- Search result redirection hack: Redirection occurs only when your website is opened via search engines.
Now that you know a lot about the WordPress redirection hack, let’s proceed with the hack removal measures.
How to fix the WordPress redirect hack
To fix the WordPress redirection hack, you need to take the following steps:
- Scan your website
- Clean malware infection
- Remove suspicious users, plugins, and themes
- Update credentials, plugins and themes
In the next few sections, we will show how to carry out each of these steps. Let’s get started. 🎬
Step 1: Scan your website 🔎
The first thing you need to do is identify malware-infected files and folders present on your WordPress website. This can be done manually or using a security plugin or dedicated malware scanner.
Manually scan your site
Manual scanning is difficult because it requires technical knowledge.
First off, you need to know your way around the backend of a WordPress website. You should be able to access the public_html folder and check the files and folders inside that particular folder.
And second, you should be able to tell the difference between a clean code and a malicious one. This can be tricky for even veteran developers.
Hackers are smart, they have honed the technique of hiding malicious codes, files, and folders in plain sight. So even if we were to guide you through the manual scanning process, you could end up deleting the wrong code snippet, file, or folder and crashing your website.
Scanning your hacked site with a security plugin is a much safer way to identify malware infection.
Scan your site with a security plugin
There are dedicated scanning plugins available out there, but we recommend using a security plugin. It’s because scanners only scan the site, whereas security plugins help clean a hacked site after identifying the malware as well.
There are several security plugins to choose from. Select a plugin, install it on your website, and initiate the scan. Just be sure to consider which plugin to use carefully.
You will want to select one that’s not too costly and does not have a long turnover time. Also, look into the scanning and malware removal process of the plugins before making your choice.
For instance, Wordfence allows you to launch a scan from within your WordPress dashboard. But, with a security plugin like MalCare, you need to access their external dashboard and then add your website to that dashboard before proceeding with a scan.

MalCare allows you to start running the cleaner immediately after the scan is over. But most security plugins will need you to wait for their malware removal experts to access your website and clean it. This indicates that MalCare will clean your website faster than any other security plugin.
Select a security plugin after considering the pros and cons of all of them. Then proceed to get your website scanned with the plugin of your choice.
Step 2: Clean malware infection 🧹
The malware removal process for most security plugins looks like this…
After scanning your site, the plugin displays infected files found on your website.
They then urge you to contact their malware-cleaning experts by raising a ticket or by hitting the Clean Site button.
Next, you need to give access to your website and wait for 24 hours for the malware removal team to clean up infected files and folders.
While most malware removal processes look like this, some security plugins like MalCare offer immediate cleanups. All you need to do is to begin the process by selecting the Auto Clean button and entering your site’s FTP credentials to allow the automated system to access your website. Then just sit back and wait for a few minutes while your website is being cleaned.
If you’re using managed WordPress hosting, your hosting provider might also offer a free service to fix a hacked WordPress site. This is true of most high-quality managed WordPress hosts.
Step 3: Remove suspicious users, plugins, and themes 🗑
After gaining access to your website, hackers infect your files and folders as well as add malicious users, plugins, and themes to the site. They use this software to get access to your website after the site has been cleaned.
To prevent a re-hack, you need to examine all existing users, plugins, and themes carefully. Don’t hesitate to remove any user or software that looks suspicious.

Step 4: Update credentials, plugins, and themes 🧑💻🔌🎨
Earlier in this article, we mentioned how the common causes of the WordPress redirect hack are outdated and nulled plugins and themes as well as weak user credentials.
After removing malware infection and malicious users or software from your website, you need to remove the real cause of the hack.
This can be done by updating outdated plugins and themes, making it mandatory to use strong credentials, and removing nulled plugins and themes for good.
How to prevent WordPress redirect hacks in the future
To prevent redirect hacks or any other types of hacks in your WordPress website, you need to take the following steps:
That’s it. With that, we have come to the end of this tutorial. 😼
Last word on the WordPress redirect hack 🏁
The WordPress redirect hack is commonly caused due to outdated or nulled plugins and themes, weak usernames, and passwords.
Removing the hack manually is a laborious process and requires technical knowledge, which is why using a security plugin is the best way to clean this type of hack.
After cleaning the hack, it’s important to prevent a re-hack. You can do this by taking steps, like removing suspicious users, plugins, and themes, removing nulled plugins and themes, and updating outdated plugins and themes. In addition to all this, you should also install a firewall, review user roles, and implement site hardening measures.
If you still have any questions about the WordPress redirect hack, let us know in the comment section below.
